The Windows Utilities Developer Forum IObit was hacked last weekend and used for spreading the unusual DeroHE ransomware among the participants.
IObit is a software developer known for its Windows system optimization and anti-malware programs such as Advanced SystemCare.
Over the weekend, members of the IObit forum began receiving emails, purportedly from IObit, saying they were eligible for a free one-year license for their software as a reward for their active participation in the forum.
“A few weeks ago, I registered to the IOBit Software Support Forums to report a bug in their software. Yesterday, I received an email (appearing to be) from them awarding forum members “a free 1-year license” with download link. I’m usually a tech-savvy guy and know better to download/run strange software, but everything looked legit (email address, artwork, link on their URL), so I downloaded the “freebie” patch that all alleged to register my IOBit software. Hours later, my computer was completely trashed”, — write a user with the nickname Mugsy323 on the Bleeping Computer forum.
The IObit ‘Promo’ email contains a GET NOW link, which redirects to hxxps://forums.iobit.com/promo.html. This page no longer exists, but at the time of the attack, it distributed the file at hxxps://forums.iobit.com/free-iobit-license-promo.zip.
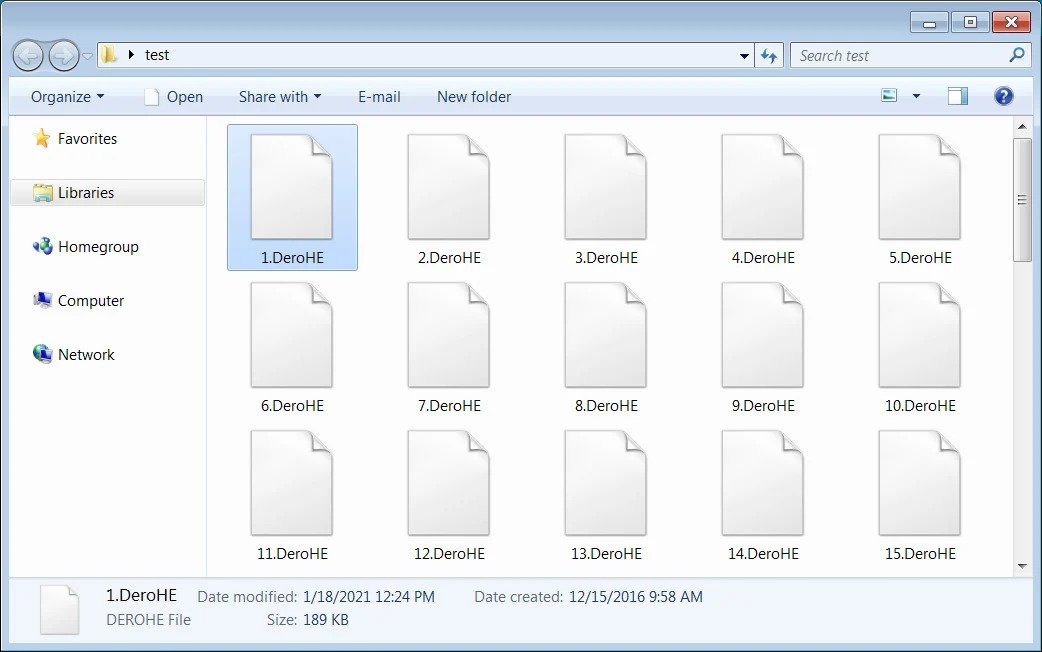
This zip archive contains digitally signed files from the legitimate IObit License Manager program, but with replaced IObitUnlocker.dll by an unsigned malicious version.
When IObit License Manager.exe is launched, the malicious IObitUnlocker.dll will be launched to install the DeroHE ransomware.
Since most of the executables were signed with an IOBit certificate and the zip file was hosted on their website, users installed the ransomware thinking it was legitimate advertising.
Emsisoft analyst Elyse van Dorp explained that the ransomware adds exceptions to Windows Defender, therefore enabling the run of the malicious library.
The ransomware displays a message box allegedly from the IObit License Manager: “Please wait. This may take a little longer than expected. Don’t turn off your computer or turn on your screen!”
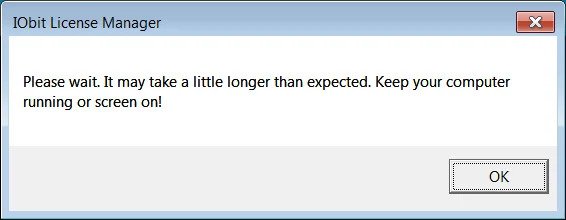
The ransomware displays this warning to prevent victims from disconnecting their devices until they finish encrypting their computers.
On the Windows desktop, the DeroHE ransomware will create two files named FILES_ENCRYPTED.html containing a list of all encrypted files and a ransom note READ_TO_DECRYPT.html.
The ransom note is titled “Dero Homomorphic Encryption” and promotes a cryptocurrency called DERO. In this note, the victim is asked to send 200 coins worth about $100 to the specified address in order to receive a decoder.
Interestingly, the attackers also send a link to a message that can only be opened by the Tor website, which says that IObit can send $100,000 in DERO coins to decrypt all victims since IObit is guilty of compromise.
“Tell iobit.com to send us 100,000 (1 hundred thousand) DERO coins to this address. After receiving the payment, the entire encrypted computer (including yours) will be decrypted. THIS IS THE IOBIT ERROR caused your computer to get infected”, — says the DeroHE Tor payment site.
Information security specialists analyze malware for weaknesses, but it is not yet known whether they will be able to detect them.
Let me remind you that The Gitpaste-12 malware is distributed via GitHub and Pastebin.








