Last week, I saw a plenty of messages like “my internet browser displays me undesirable Wedger.live pop-up promotions, is it a computer virus?” or “these Wedger.live pop-up ads in my Chrome making me insane, how to deal with them?”. According to the statistics for last months, virus suppliers began a wide adware distribution project. Let me demonstrate you, how you can eliminate the pc virus from your PC, and also forget about the frustrating Wedger.live pop-ups.





Pop-Ups : Discovering The Nature
You can admit that some sites (like a Wedger.live) show you pop-up ads. The message can contain something like “do you want to have notifications about the most up to date news?” or “allow alerts to be reported about latest price cuts?”. Generally, such messages are safe, and can just distract you with its unexpected showing up. Moreover, it can be simply turned off, in case alerts from this web site are no longer needed.
Pop-up notices are rather an efficient advertising tool. If you want products of some type, you can allow pop-ups from the web site where you can acquire this things, and also as quickly as these products are in inventory again, or if you can have a price cut – you will certainly get the alert about this. The counterparty – online sellers, vehicle lending services, etc – will be in profit, too – buyer will undoubtedly obtain a tip about the product he/she planned to pay for. And also such an advertising and marketing method is almost free – this element is extremely essential for companies.
| Site | Wedger.live |
| IP Address | 157.230.4.182 |
| Infection Type | Adware, Push notifications, Unwanted Ads, Pop-up Ads |
| Symptoms | Annoying pop-up ads in the right corner. |
| Similar behavior | Smalk.live, Tuskel.live, News-xufiyu.cc |
Wedger.live Pop-Ups Are Not So Safe
But often pop-up ads can come out without your approval, and also with a content which is completely different from your current interests or search questions. And also, besides undesirable Wedger.live pop-ups from the unknown website, you can simultaneously see a great deal of promotions, including ones on the pages which primarily have no ads whatsoever. Such a situation can be the sign of adware presence.
Adware is the sort of pc virus which injects into your computer, after that starts displaying you various promotions. Their subject usually has no correlation with your normal search queries. Besides banner promotions, your web browser can additionally show you a massive quantity of different Wedger.live pop-up promotions, which appear in the bottom right corner.
The model of adware use is really sly. The huge pack of adware is dispersed through trojan viruses, which are injected in your desktop previously. Advertisements, which are displayed to you by virus, are paid by their makers. In several weeks, all antivirus programs began to catch these adware, hence, trojan loses in earnings. And to finish the user’s computer, malware distributors begin ransomware distribution via these trojans.
Even if there is no active ransomware distribution, your PC might continue to be influenced by adware virus. A huge amount of ads together with Wedger.live pop-ups can make your PC as slow as snail, so your normal activities will certainly be impossible to do in normal manner.
How Can I Deal With Wedger.live Pop-Ups?
Thinking the paragraphs above: your computer, and your information, is in a serious danger. To stop this infection, you require to use anti-malware tool. Microsoft Defender, which is installed in every Windows 10 distribution, has the ability to deal with Wedger.live pop-ups malware. However, it can’t revert the web browser changes which were applied by harmful program. An additional negative aspect of the antivirus by Microsoft is its certain susceptability: malware can disable Microsoft Defender via the Group Policies after being injected to your PC.
To be 100% sure that your computer is clean of any malware now, and will be clean in future, I can offer you to use GridinSoft Anti-Malware.
To detect and eliminate all malicious programs on your PC, including Wedger.live pop-ups virus, with GridinSoft Anti-Malware, it’s better to use Standard or Full scan. Quick Scan is not able to find all the malicious programs, because it checks only the most popular registry entries and folders.
You can see the detected viruses sorted by their possible harm till the scan process. But to choose any actions against the viruses, you need to hold on until the scan is finished, or to stop the scan.
![]()
To set the action for each detected malicious or unwanted program, click the arrow in front of the name of detected malicious program. By default, all malware will be removed to quarantine.

Reset browser settings to original ones
To reset your browser settings, you are required to use the Reset Browser Settings option. This action cannot be intercepted by Wedger.live malware, hence, you will surely see the result. This option can be located in the Tools tab.

After pressing the Reset Browser Settings button, the menu will be displayed, where you can specify, which settings will be reverted to original.

Reset browser setiings without utilizing third-party applications
Besides using anti-malware tools for browser restoration, you can choose the “Reset browser settings” option, which is usually embedded in all popular browsers.
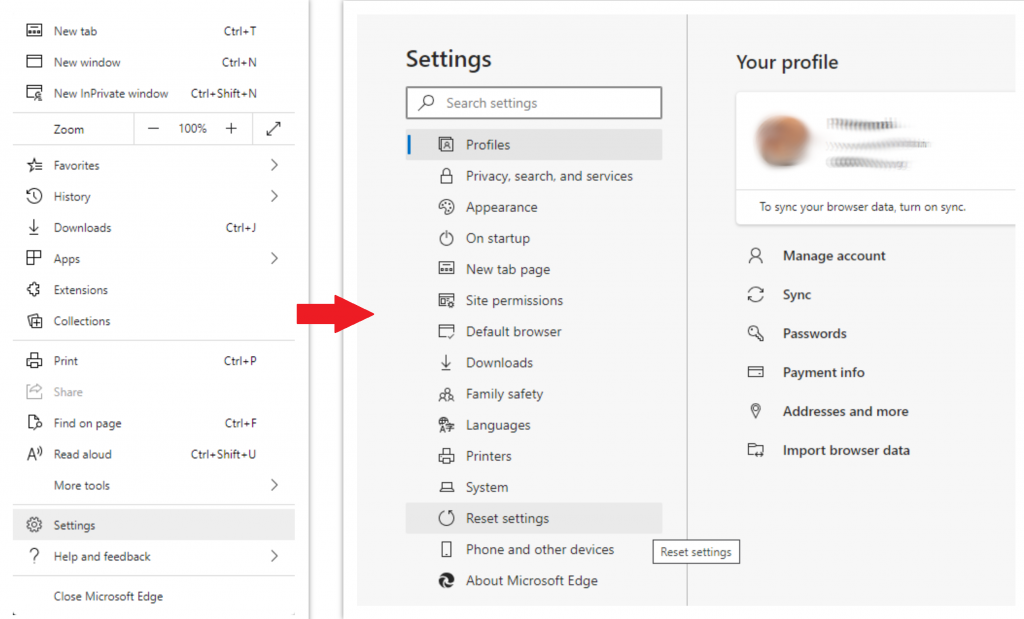
Reset Microsoft Edge  Settings
Settings
- Open "Settings and more" tab in upper right corner, then find here "Settings" button. In the appeared menu, choose "Reset settings" option:
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original:
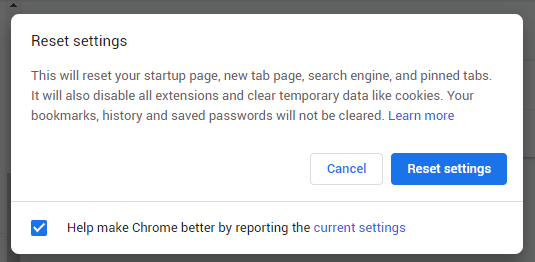
Reset Mozilla Firefox  Settings
Settings
- Open Menu tab (three strips in upper right corner) and click the "Help" button. In the appeared menu choose "troubleshooting information":
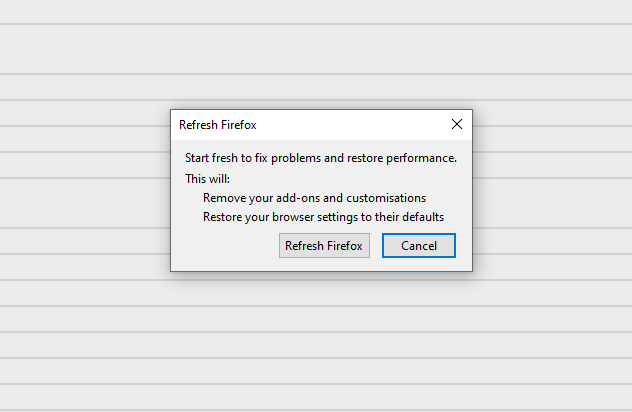
- In the next screen, find the "Refresh Firefox" option:
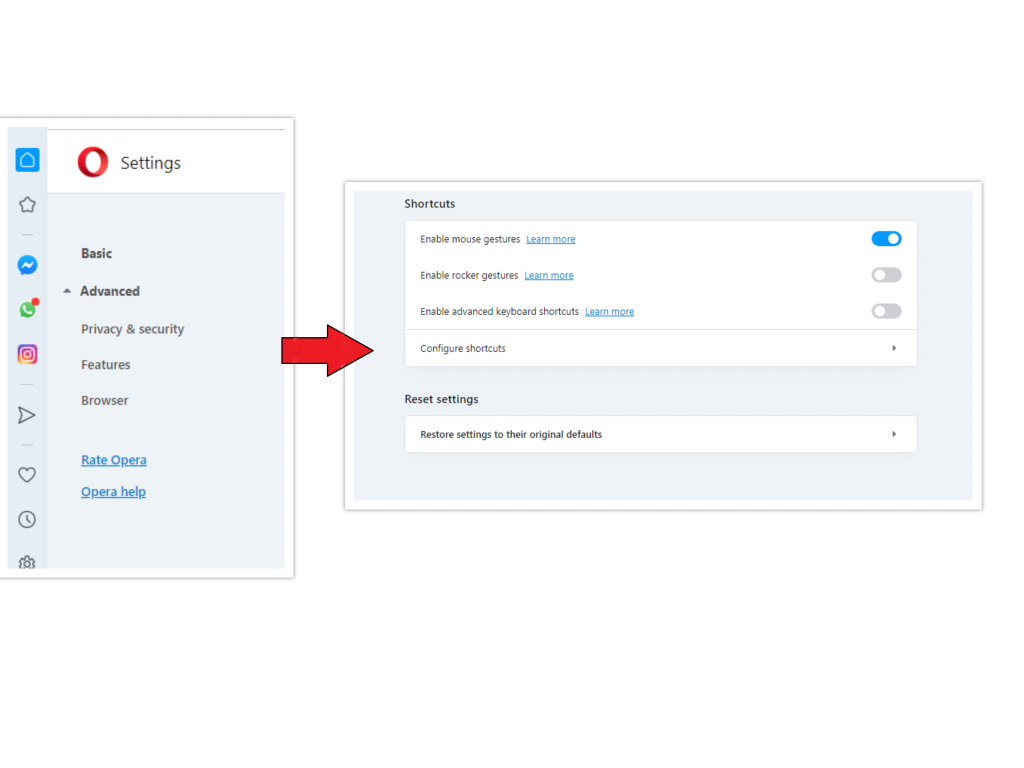
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click "Advanced" option, and choose "Browser" button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there "Restore settings to their original defaults" option:
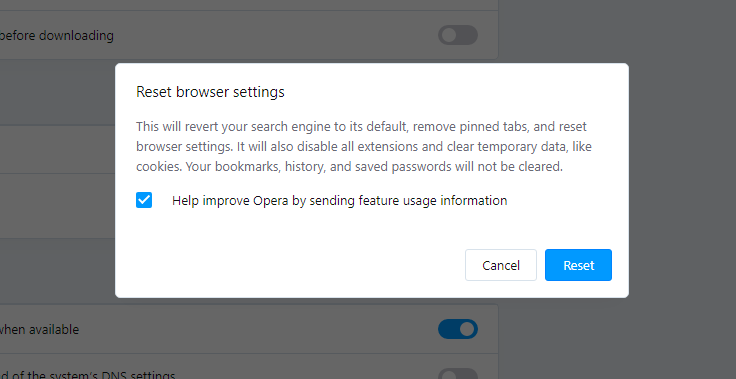
- After clicking the "Restore settings..." button, you will see the window, where all settings, which will be reset, are shown:
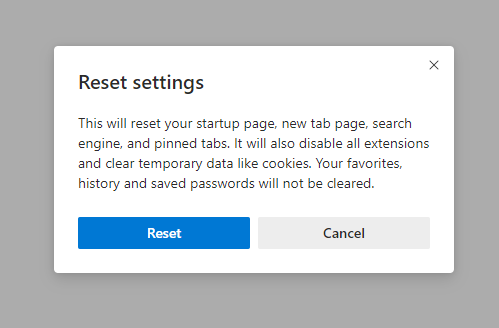
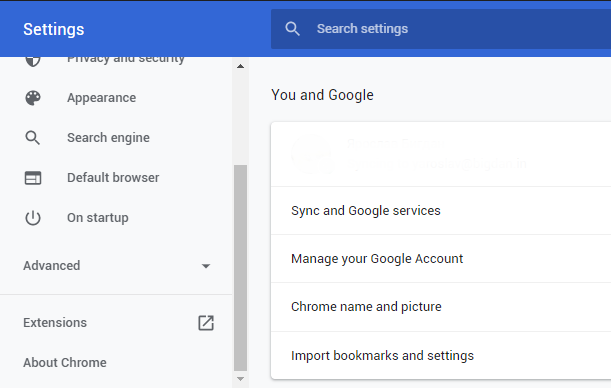
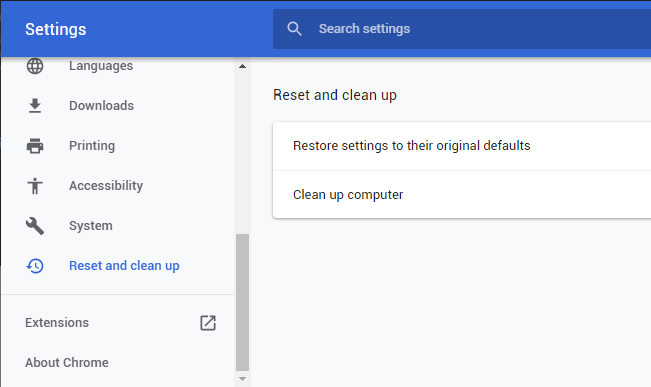
- Open Settings tab, find the "Advanced" button. In the extended tab choose the "Reset and clean up" button:
- In the appeared list, click on the "Restore settings to their original defaults":
- Finally, you will see the window, where you can see all the settings which will be reset to default:
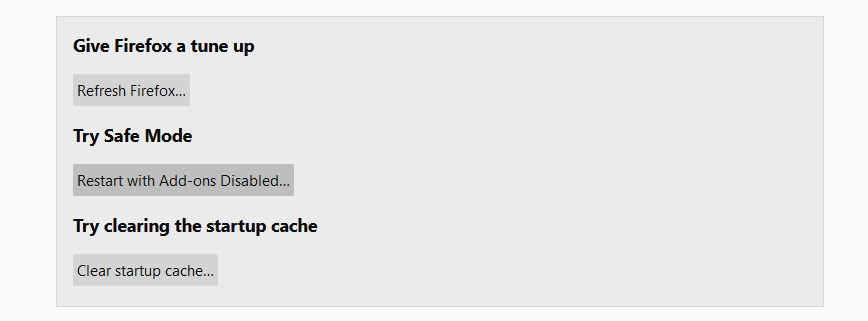 After choosing this option, you will see the next message:
After choosing this option, you will see the next message:
Reset Opera  Settings
Settings
Reset Google Chrome  Settings
Settings
As an afterword, I want to say that the time plays against you and your PC. The activity of browser hijacker Wedger.live must be stopped as soon as possible, because of possibility of other malware injection. This malware can be downloaded autonomously, or offered for you to download in one of the windows with advertisements, which are shown to you by the hijacker. You need to act as fast as you can.









