Recently, I saw a great deal of messages like “my web browser shows me undesirable News-legija.cc pop-up advertisements, is it a computer virus?” or “these News-legija.cc pop-up promotions in my Chrome making me crazy, how to manage them?”. Due to the stats for last months, virus distributors began a large adware circulation project. Let me demonstrate you, how you can delete the pc virus from your PC, as well as forget about the irritating News-legija.cc pop-ups.
Pop-Ups : Discovering The Nature
You can admit that some websites (like a News-legija.cc) offer you pop-up promotions. The message can have something like “do you want to get alerts about the current news?” or “allow notifications to be reported regarding new price cuts?”. Normally, such messages are safe, and can just distract you with its abrupt showing up. And it can be quickly turned off, in case notices from this online resource are no longer wanted.
Pop-up notifications are rather an reliable advertising mechanism. If you are interested in goods of some type, you can give a permission to the pop-ups from the site where you can purchase this stuff, and also as soon as these products are in store again, or if you can have a discount – you will get the alert concerning this. The counterparty – online sellers, cars and truck lending services, etc – will remain in profit, too – buyer will surely obtain a pointer about the item he/she intended to buy. And also such an advertising and marketing technique is almost free of charge – this aspect is really vital for firms.
| Site | News-legija.cc |
| IP Address | 149.7.16.209 |
| Infection Type | Adware, Push notifications, Unwanted Ads, Pop-up Ads |
| Symptoms | Annoying pop-up ads in the right corner. |
| Similar behavior | Cityratetod.live, Gider.live, Giney.live |
News-legija.cc Pop-Ups Are Not So Safe
However often pop-up ads can show up without your permission, as well as with an information which is totally different from your present interests or search queries. And also, besides unwanted News-legija.cc pop-ups from the unknown source, you can at the same time see a lot of promotions, including ones on the web pages which primarily have no advertisements whatsoever. Such a situation can be the trace of adware appearance.
Adware is the sort of malware which injects into your computer, after that begins displaying you various ads. Their subject often has no match with your ordinary search questions. Besides banner advertisements, your browser can likewise suggest you a big quantity of different News-legija.cc pop-up promotions, which show up in the bottom right area.
The model of adware use is very sly. The huge pack of adware is dispersed through trojan viruses, which are infiltrated in your desktop earlier. Promotions, which are suggested to you by malware, are paid by their creators. In a couple of weeks, all anti-malware programs began to stop these adware, therefore, trojan loses in productivity. And to finish the user’s desktop, virus distributors start ransomware distribution via these trojans.
Even if there is no active ransomware distribution, your computer system can continue to be affected by adware virus. A huge quantity of ads in addition to News-legija.cc pop-ups can make your PC as slow-moving as snail, so your normal work will certainly be difficult to carry out in normal manner.
How Can I Deal With News-legija.cc Pop-Ups?
Thinking the text above: your desktop, as well as your data, is in a serious risk. To quit this infection, you need to utilize antivirus software. Microsoft Defender, which is embedded in every Windows 10 distribution, has the ability to handle News-legija.cc pop-ups malware. However, it can’t change the browser alterations which were put into effect by malicious program. One more drawback of the anti-virus by Microsoft is its particular vulnerability: viruses can disable Microsoft Defender with the Group Policies after being implanted to your desktop.
To be 100% sure that your PC is clean of any malware now, and will be clean in future, I can advice you to use GridinSoft Anti-Malware.
To detect and remove all unwanted applications on your desktop, including News-legija.cc pop-ups virus, with GridinSoft Anti-Malware, it’s better to utilize Standard or Full scan. Quick Scan is not able to find all the malware, because it scans only the most popular registry entries and directories.
You can observe the detected malicious apps sorted by their possible hazard till the scan process. But to perform any actions against malware, you need to hold on until the scan is over, or to stop the scan.

To choose the action for every detected virus or unwanted program, click the arrow in front of the name of detected malware. By default, all the viruses will be removed to quarantine.

Reset browser settings to original ones
To reset your browser settings, you need to use the Reset Browser Settings option. This action cannot be intercepted by News-legija.cc virus, hence, you will surely see the result. This action can be found in the Tools tab.

After pressing the Reset Browser Settings button, the menu will be displayed, where you can specify, which settings will be reverted to original.

Reset browser setiings without utilizing third-party programs
Besides using antivirus software for browser restoration, you can choose the “Reset browser settings” option, which is usually embedded in all popular browsers.
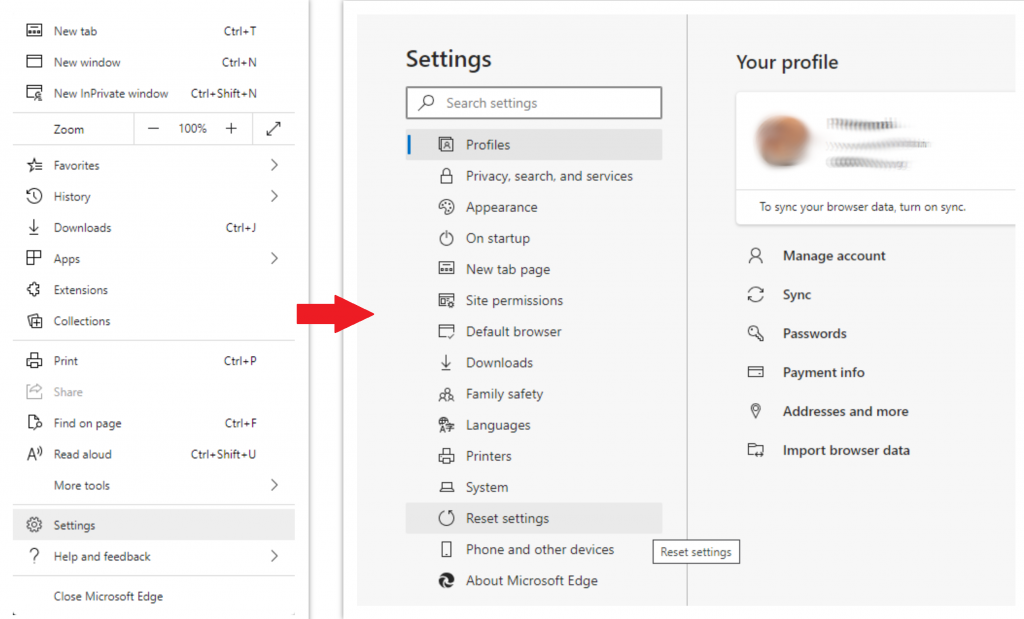
Reset Microsoft Edge ⚙ Settings
- Open "Settings and more" tab in upper right corner, then find here "Settings" button. In the appeared menu, choose "Reset settings" option:
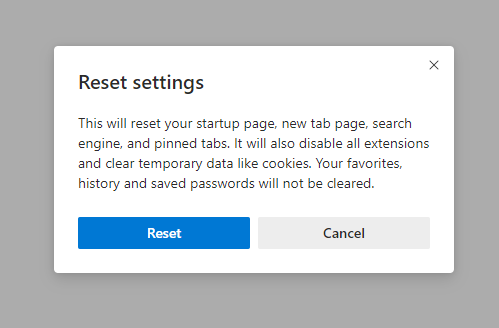
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original:
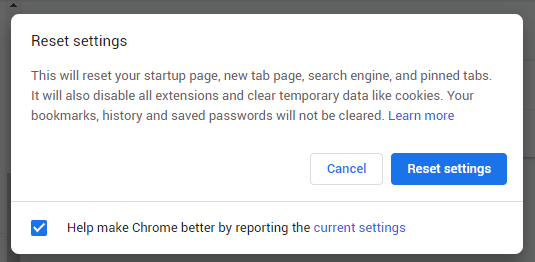
Reset Mozilla Firefox ⚙ Settings
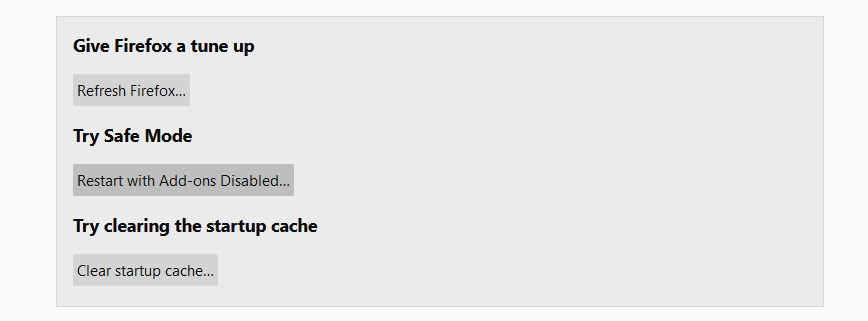
- Open Menu tab (three strips in upper right corner) and click the "Help" button. In the appeared menu choose "troubleshooting information":
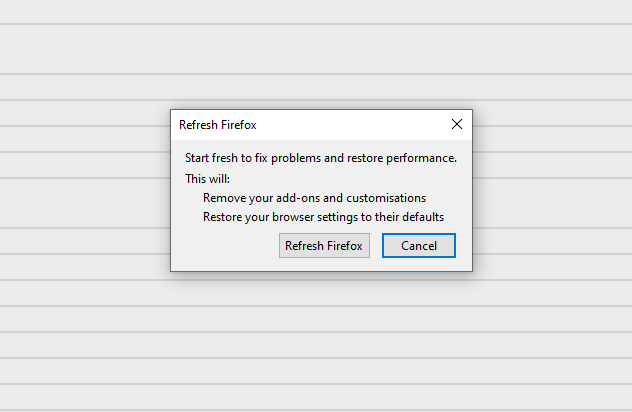
- In the next screen, find the "Refresh Firefox" option:
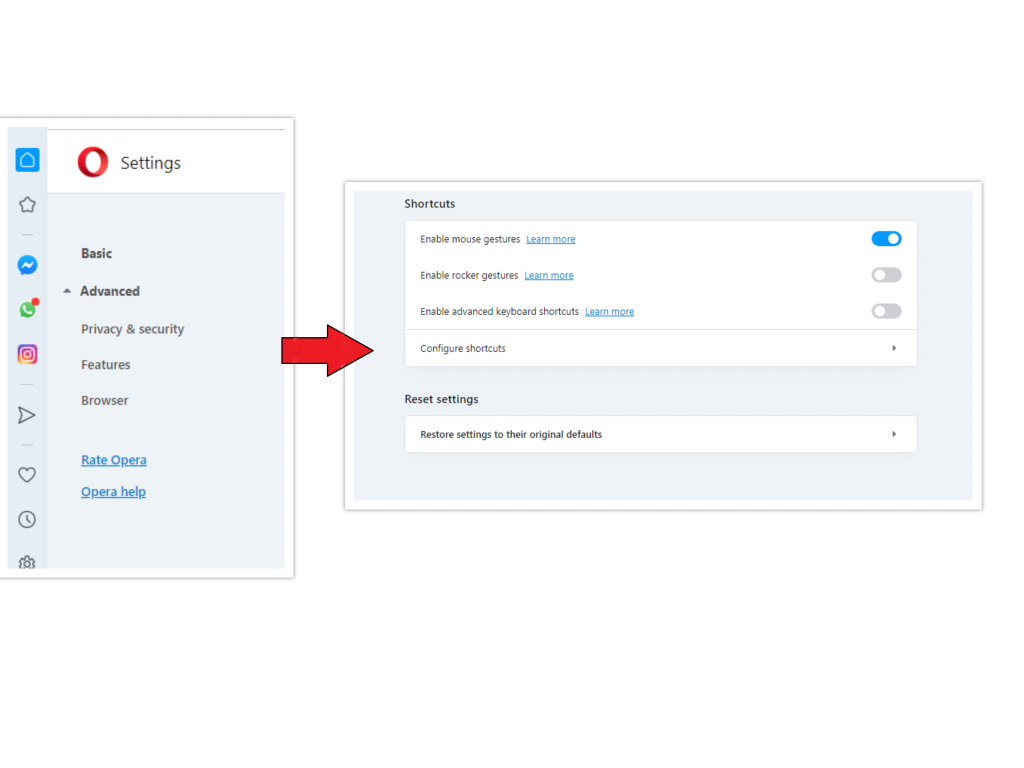
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click "Advanced" option, and choose "Browser" button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there "Restore settings to their original defaults" option:
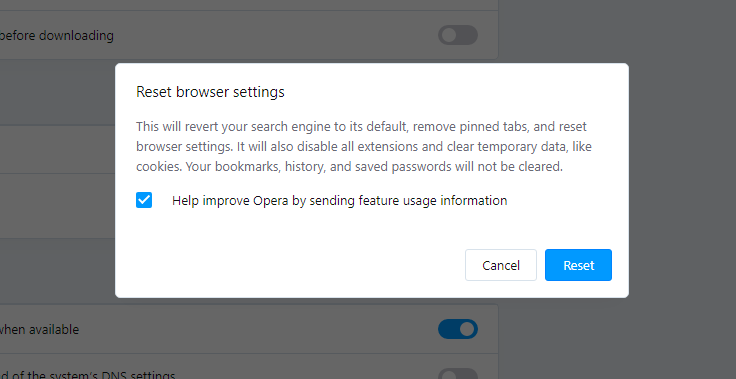
- After clicking the "Restore settings..." button, you will see the window, where all settings, which will be reset, are shown:
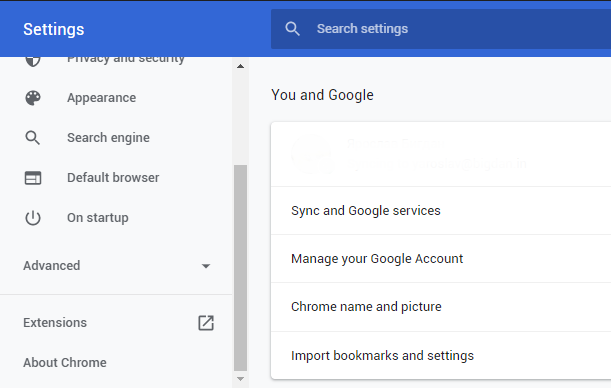
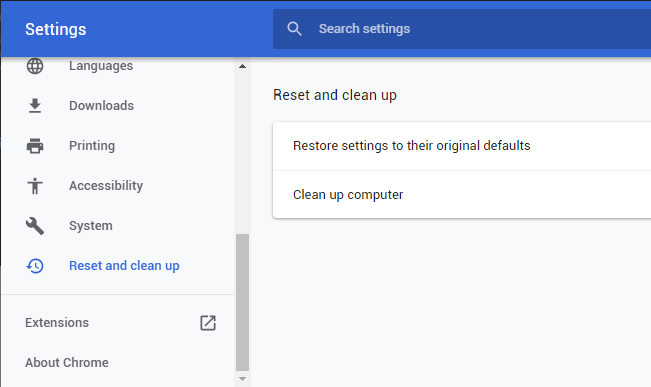
- Open Settings tab, find the "Advanced" button. In the extended tab choose the "Reset and clean up" button:
- In the appeared list, click on the "Restore settings to their original defaults":
- Finally, you will see the window, where you can see all the settings which will be reset to default:
 After choosing this option, you will see the next message:
After choosing this option, you will see the next message:
Reset Opera ⚙ Settings
Reset Google Chrome ⚙ Settings
As an afterword, I want to say that the time plays against you and your PC. The activity of browser hijacker News-legija.cc must be stopped as soon as possible, because of possibility of other malware injection. This malware can be downloaded autonomously, or offered for you to download in one of the windows with advertisements, which are shown to you by the hijacker. You need to act as fast as you can.











