According to Microsoft and Sophos experts, cybercriminals use black-hat SEO techniques to spread Gootloader malware.
The researchers report that the Gootkit info-stealer has evolved into a complex and secretive framework, which is now called Gootloader. The malware spreads a wide range of malware through hacked WordPress sites, abusing so-called black SEO techniques.
It is noted that not only the number of payloads has increased: Gootloader distributes payloads across several regions and hundreds of hacked servers, which are always active.
“Gootloader currently controls about 400 servers hosting hacked legitimate sites”, — the researchers report.
Last year, experts first noticed malicious campaigns based on the Gootloader mechanism. Then they were in charge of delivering the REvil ransomware and mainly attacked targets in Germany. This marked a kind of new start for Gootkit, since before that the malware was inactive after a data leak that its operators allowed in 2019.
Now the hackers have regrouped, built a vast network of hacked WordPress sites, and used various SEO techniques to display fake forums with malicious links on Google.
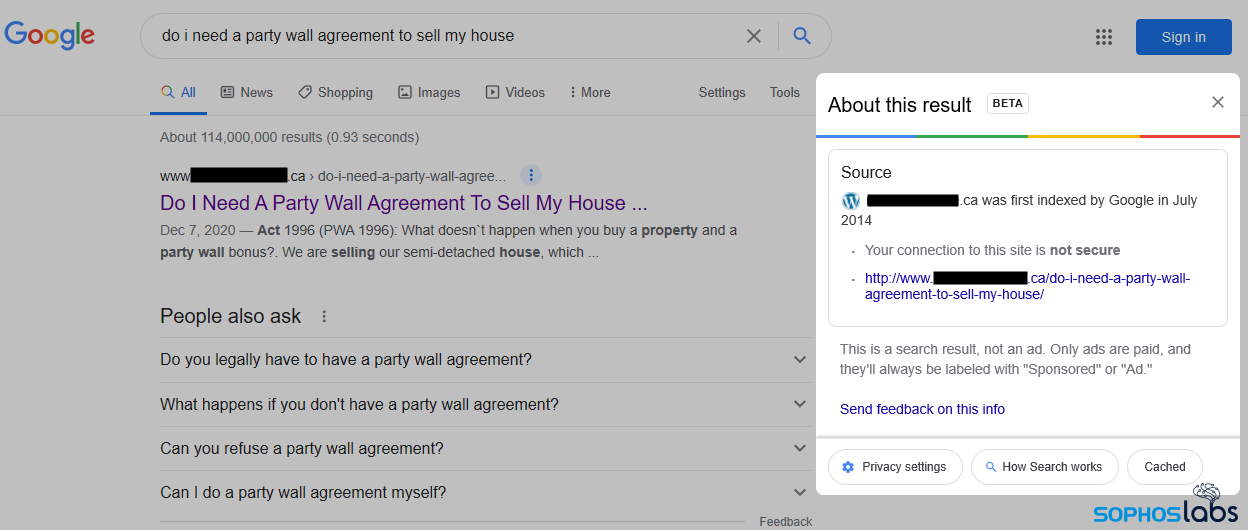
Such fake forums are only visible to users from certain regions. These “discussions” supposedly contain a response to a specific user request. Moreover, the response message is published on behalf of the site administrator, and contains a malicious link. To show potential victims such fake discussions, hackers modify the CMS of the compromised resources.
The example below shows how a fake forum post responds to a specific search query related to real estate transactions. Moreover, this “discussion” takes place on a site about neonatal medicine, which has nothing to do with the topic, “however, this is the first result that appears when a certain type of real estate agreement is requested,” experts say.
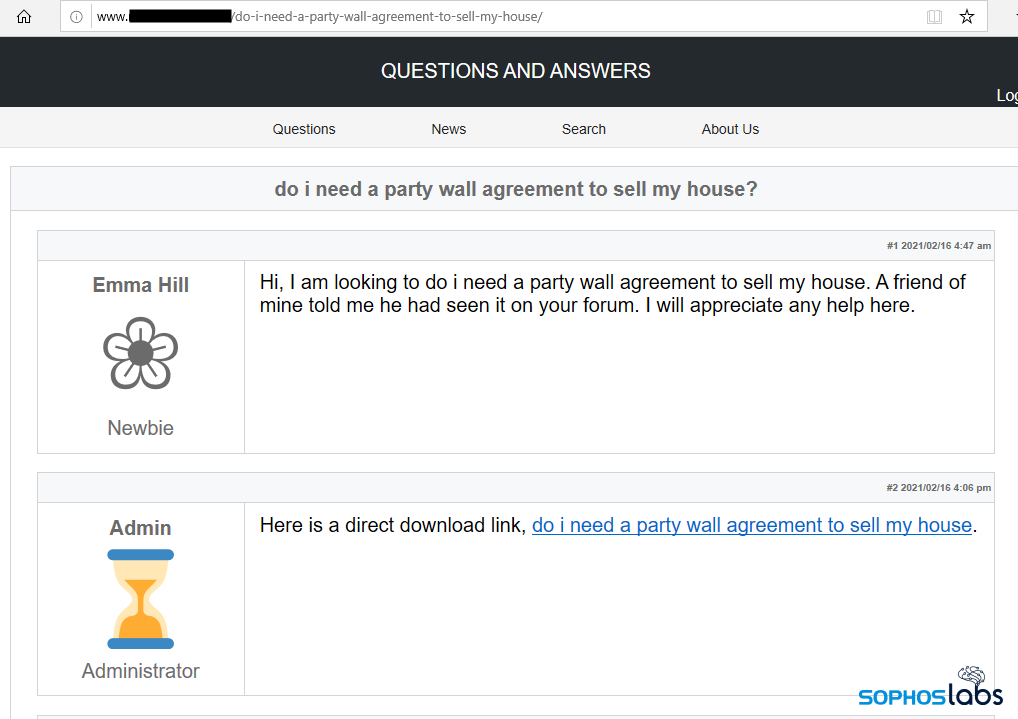
When clicking on such a link from the “forum”, the visitor receives a ZIP archive with a JavaScript file that starts the infection process. It is noted that this is the only stage, at which the file is written to disk, all other operations are performed by the malware in memory, so many security tools are useless against Gootloader.
It is reported that now, in addition to the standard payload (Gootkit and REvil ransomware), Gootloader can also distribute the Kronos and Cobalt Strike Trojan. These attacks target visitors from the United States, Germany, and South Korea.
It is not yet clear how exactly the malware operators gain access to the sites on which the fake forums are then placed. Researchers suspect that attackers may have obtained the credentials of these resources from Gootkit installations, bought them on the black market, or exploited known bugs in CMS plugins.
“The Gootkit developers seem to have redirected their resources away from delivering their own malware to creating a stealthy and sophisticated platform for delivering all kinds of payloads, including the REvil ransomware. This shows that criminals tend to reuse proven solutions rather than develop new delivery mechanisms. In addition, instead of using aggressive attacking tools, as some malware distributors do, the Gootloader authors have chosen a tortuous path of sophisticated evasion techniques that help hide the end result”, — Sophos experts conclude.
Let me remind you that I also talked about the fact that The number of malware written in Go has increased by 2000% in a few years.









