Doctor Web experts have found various malware in the AppGallery, an official catalogue of applications for Huawei devices, as multifunctional Trojans of the Android.Joker family that subscribe users to paid mobile services.
In total, experts found 10 modifications of these Trojans in AppGallery, which were downloaded by over 538,000 Android device owners.
The Android.Joker family has been known to specialists since the fall of 2019, and analysts discover new versions and modifications of these Trojans almost every day. Typically, such malware is capable of performing various tasks (depending on the goals of the attackers).
“For example, the decoys that victims install are usually basic modules with minimal functionality. They only provide communication between other Trojan components. In this case, the main malicious tasks are performed by modules that are later downloaded from the Internet”, — information security experts say.
Previously, applications infected with Android.Joker were found mainly in the official catalog of Android applications on Google Play. Now, however, the attackers seem to have decided to expand their activities and turned their attention to alternative directories supported by major players in the mobile device market.
As with other versions of this malware, modifications found in AppGallery were distributed under the guise of harmless applications that after launching worked as expected by users. This technique allows virus writers to remain undetected for longer and infect as many devices as possible.
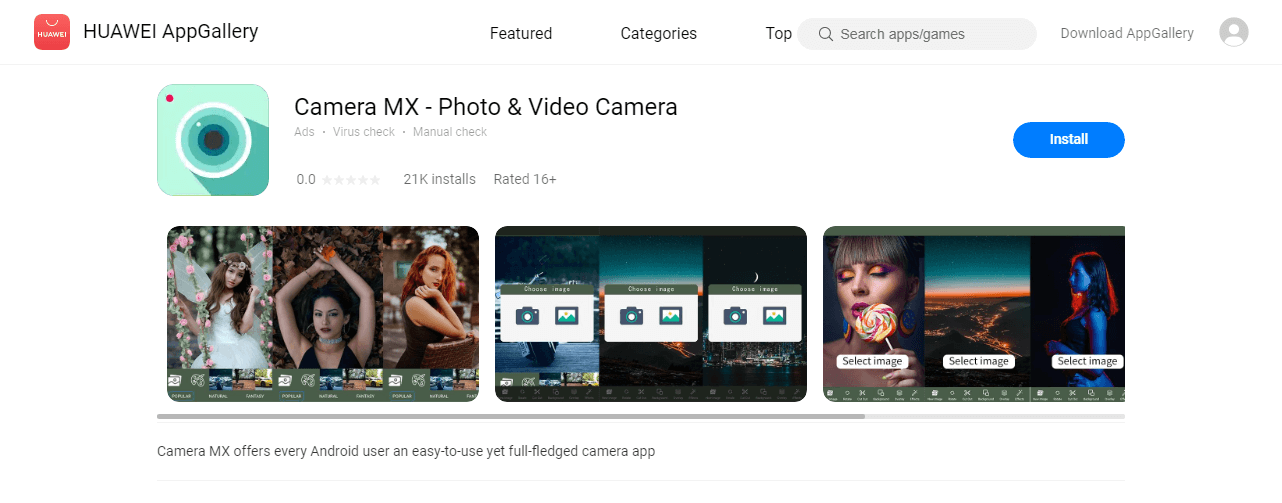
The identified Trojans were hidden in virtual keyboards, a camera application, a launcher, a messenger, a collection of stickers, coloring programs, as well as in the games.
After downloading and starting such an application, users do not notice anything strange, while Android.Joker invisibly connects to the control server, receives the necessary settings and downloads one of the auxiliary components, which it then launched.
The downloadable component is responsible for the automatic subscription of Android device owners to expensive mobile services. In addition, decoys ask for access to notifications, which they need to intercept SMS from premium services (with subscription activation confirmation codes).
The downloadable module is detected by Doctor Web as Android.Joker.242.origin. Similarly marked other modules that load all 10 new malware modifications.
Android.Joker.242.origin connects to a remote hacker server and requests configuration from it. It contains a list of tasks with premium service sites, JavaScript scripts used to simulate user actions on these sites, and other parameters.
For each task, the module creates an “invisible” WebView and sequentially loads a paid service site in each of them. After that, the Trojan downloads JavaScript and uses it to independently click on buttons in the web form, automatically substituting the victim’s phone number and PIN code for confirmation, intercepted by another basic module, for example, Android.Joker.531.
Worse, the malware hunts not only for activation codes, but also sends the contents of all notifications about incoming SMS to the attacker’s server, which can lead to leakage of confidential information.
“After receiving an alert from Doctor Web, Huawei hid malware applications in the AppGallery app store to ensure user safety. The company will conduct an additional check in order to minimize the risks of such programs appearing in the future”, — the press service of AppGallery says.
Let me remind you that I talked about the fact that New spyware for Android pretends to be System Update.






